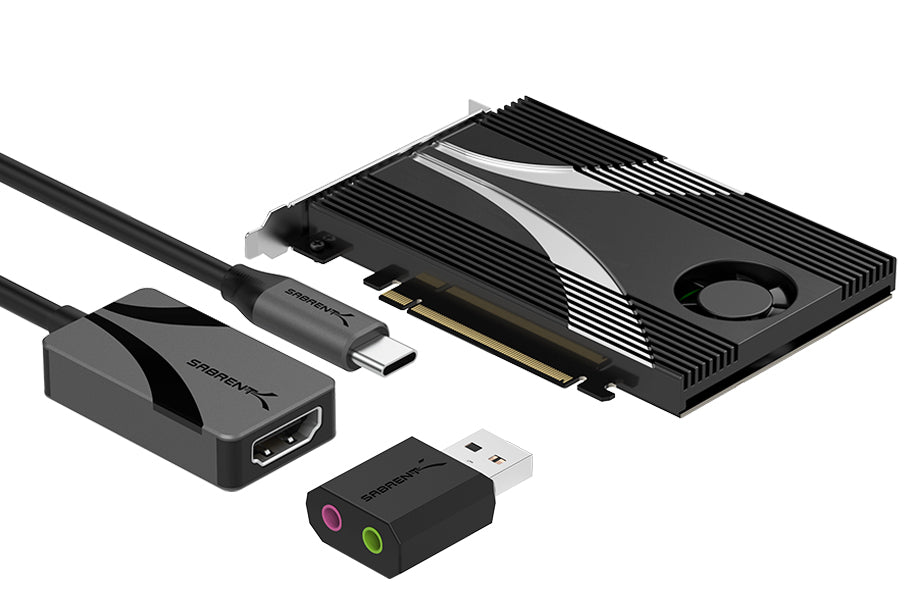
SED and NVMe in action. Source: NVM Express.

Bitlocker. Source: Windows Central.
- Make sure the drive is installed correctly. It should show up in the UEFI (BIOS) as being present. Certain machines may require adjustment or modification to show drives, especially older systems that lack native NVMe boot support.
- The Compatibility Support Module (CSM) setting is used to allow booting to legacy devices before the 2TB limit was overcome. It should be disabled for full modern functionality. Check your motherboard's manual to see this setting's location.
- You need to boot into Windows, but not on the intended target drive. You can use your existing or another drive to boot, or a bootable Windows solution such as Windows 2 Go.
- SSD vendors will have a method of enabling/disabling encryption. Usually this is in an SSD toolbox like Samsung's Magician. The target drive must had encryption enabled before anything else.
- Make sure the drive is wiped. This is usually done with a secure erase or sanitize procedure. This can be achieved in a number of ways including through the SSD toolbox, with bootable tools like Parted Magic or nvme-cli, with native OS tools, or through the UEFI.
- This is a step that's often missed. Systems with encryption will have a Trusted Platform Module (TPM) that's used for security purposes and required for a modern Windows 11 installation. The UEFI will have settings for the TPM which includes Block SID Authentication which is part of the TCG feature set for SEDs. This feature is protective but needs to be disabled either in the UEFI or via PowerShell in Windows or Windows 2 Go. As per the blog linked above:
- open Powershell as admin in Windows 2 Go
- Run: `$tpm = gwmi -n root\cimv2\security\microsofttpm win32_tpm`
- Run: `$tpm.SetPhysicalPresenceRequest(97)`
- Reboot
- Once it's confirmed that Block SID has been disabled on reboot, you can prepare a bootable Windows installation USB drive to start installing an OS on the target SSD. This should occur as normal on the next reboot, and you may install the OS to the drive.
- Once the installation is complete and you have booted into the new OS on the target SSD, Windows must be set up to use hardware encryption in Bitlocker, as per the linked blog:
- open "group policies" via start
- Computer configuration > administrative templates > Windows components > Bitlocker > system drive > administrative Configure use of hardware-based encryption for fixed data drives
- activate the policy and disable fallback to software encryption in the lower left.
- At this point, opening Bitlocker should enable you to encrypt the drive. You may need to re-enable the Block SID feature if you are still getting any warnings, via UEFI or:
- open Powershell as admin in Windows 2 Go
- Run: `$tpm = gwmi -n root\cimv2\security\microsofttpm win32_tpm`
- Run: `$tpm.SetPhysicalPresenceRequest(96)`
- Reboot
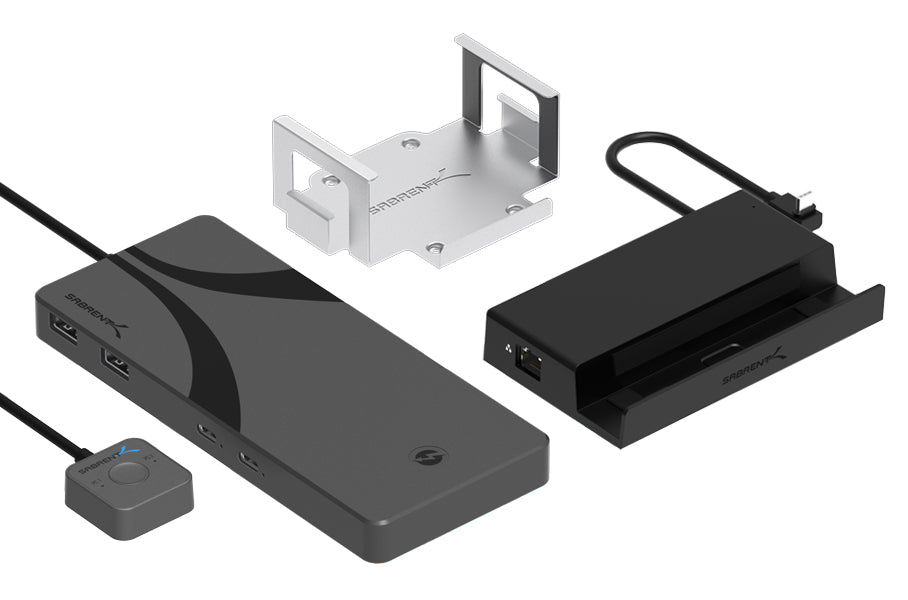
This should be sufficient to get you booted into windows on your SSD with hardware encryption enabled. The process may be made easier with storage accessories or external storage solutions. We suggest having your motherboard's manual available as a resource, whether paper or PDF, and sometimes the UEFI/BIOS manual is a separate download. Make sure to go over the entire process first in your mind and have everything prepared before starting. Good luck!